- NBA Online Betting Sites in the Philippines 2024
- About Basketball and NBA Online Betting in the Philippines
- Top NBA Online Betting Sites in the Philippines
- Factors to Consider When Choosing a best NBA Online Betting Site
- Popular payment methods for NBA betting in the Philippines
- Popular types of bets on NBA games
- How to Place NBA Bets Online in the Philippines
- Tips for Successful NBA Online Betting
- Conclusion
- FAQ about NBA Online Betting in the Philippines
NBA Online Betting Sites in the Philippines 2024
- One of the best bonus lines for new and existing customers
- Wide range of sports and betting options
- Huge number of deposit methods, including many local methods for Asian countries
- Live streaming and In-Play betting available
- Accept bettors from all Asian countries
+250 Free Spins
Promo code: ml_308595
- 40+ Sports - Cricket, soccer, rugby & tennis
- Loads of cricket betting markets
- Vast range of rupee promotions
- High withdrawal limit
- Supports local Asian payments & fast withdrawals for Malaysia, India, Bangladesh, Philippines, China, Japan
- Huge range of gambling options
Bonus Code: RM600!
- Wide range of payment methods, currencies and cryptocurrencies
- Great free bet bonus offer with no wagering requirements
- Sports betting and casino games available
- Mobile app available for convenient access
- Live support available for assistance
- Accepts credit cards
About Basketball and NBA Online Betting in the Philippines
In the Philippines, basketball isn’t just a sport—it’s a passion. The NBA, standing tall as the premier professional basketball league globally, commands a vast following in the country. This immense popularity has given rise to a thriving NBA online betting scene in the Philippines, allowing enthusiasts to back their favorite teams and stars.
What is NBA Online Betting?
Simply put, NBA online betting allows enthusiasts to wager on various NBA game outcomes and events through digital platforms, be it a sportsbook or a betting website. With just a click on their computers or a tap on their mobile devices, fans can immerse themselves in the excitement of betting, regardless of their location.
These online platforms offer a plethora of betting choices ranging from moneyline bets, point spread bets, and totals bets to futures bets and beyond. Additionally, for those who love the thrill of making decisions on the spot, some platforms offer live betting, letting users place bets in real-time as the game unfolds.
Is NBA Online Betting Legal in the Philippines?
For Filipino basketball enthusiasts pondering over the legality of NBA online betting, rest assured—it’s both legal and exhilarating. Numerous sports betting sites cater to the NBA betting market. However, when venturing into this exciting domain, always prioritize licensed and regulated platforms to guarantee both the security of your personal information and the integrity of your wagers.
Top NBA Online Betting Sites in the Philippines
There are many sports betting sites that offer NBA online betting in the Philippines, but some of the best include:
Melbet
Melbet stands out for its competitive odds, diverse sports markets, and attractive welcome bonuses. Users can enjoy live betting on lesser-known leagues that competitors might overlook. Major credit cards, several e-wallets, and even virtual currencies like Bitcoin and Ethereum are all supported by Melbet. If you prioritize flexibility, reliability, and great user experience, Melbet could be your go-to platform.
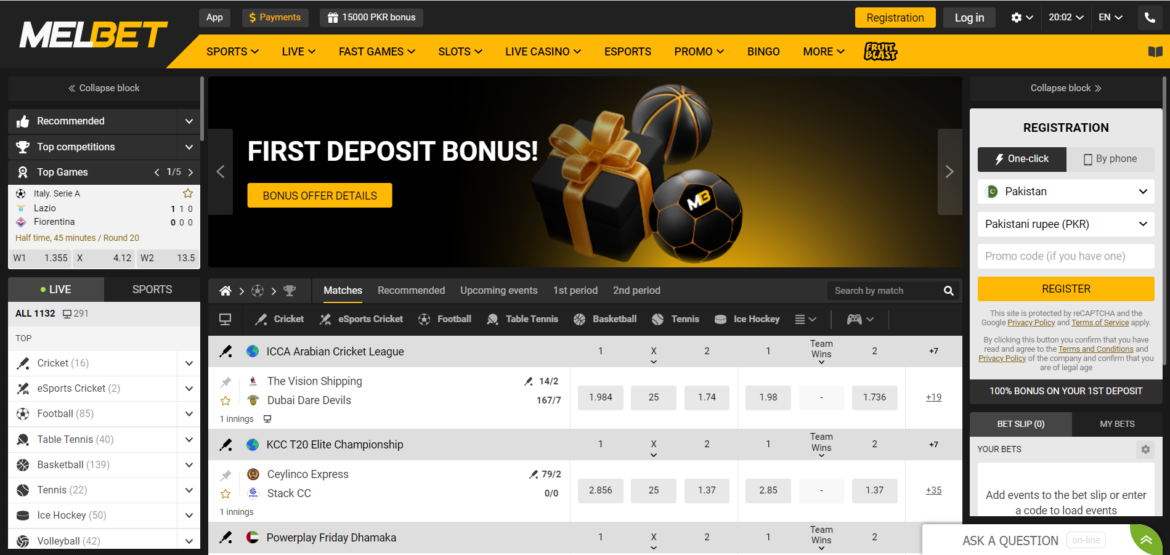
- Wide variety of NBA betting options
- User-friendly interface and mobile app
- Competitive odds.
- Limited promotions specific to NBA
- Customer support may be slower during peak times.
Sportsbet.io
Established in 2016, Sportsbet.io offers both a rapid and pleasurable betting journey. They continually roll out promotions for both rookies and regulars. A distinctive feature is their integration with the Coingaming.io Bitcoin gaming platform, meaning they primarily accept cryptocurrency payments. If you’re into diverse betting options, live play, and casino games, Sportsbet.io is worth considering.
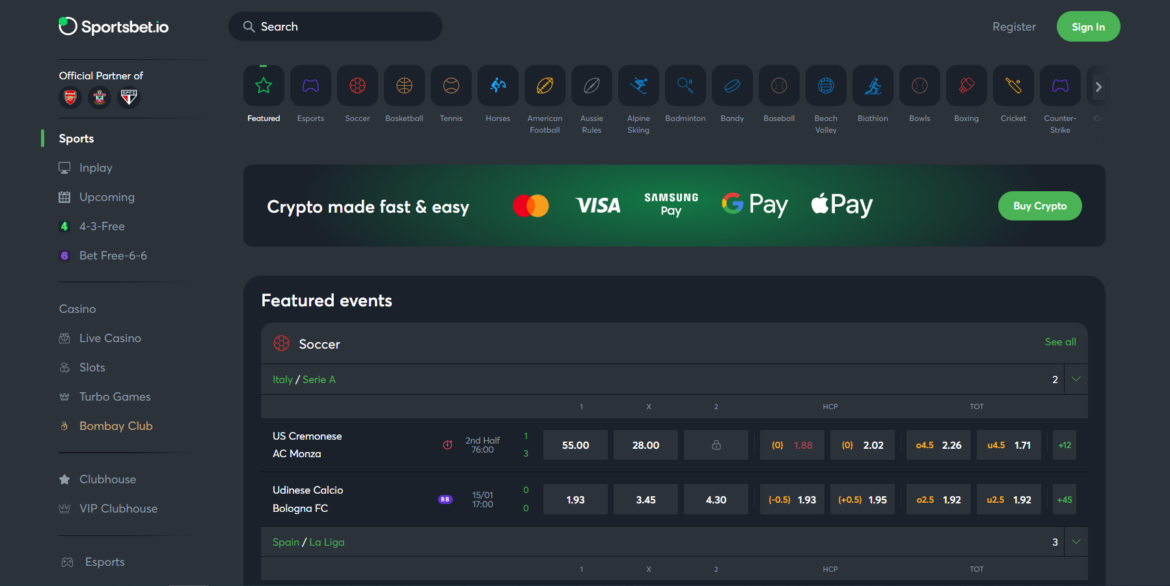
- Accepts both fiat and cryptocurrency
- Frequent promotional offers for NBA games
- Live streaming available for select matches.
- Limited coverage of lower-tier basketball leagues
- Deposit and withdrawal fees may apply.
1xBet
1xBet‘s appeal lies in its vast variety of betting events, both sports-related and others. Features like Cash Out, Bet Builder, and LIVE betting enhance the overall user experience. They offer multiple payment methods, making depositing funds a breeze. The platform’s layout is intuitive, making both navigating and betting a seamless experience.
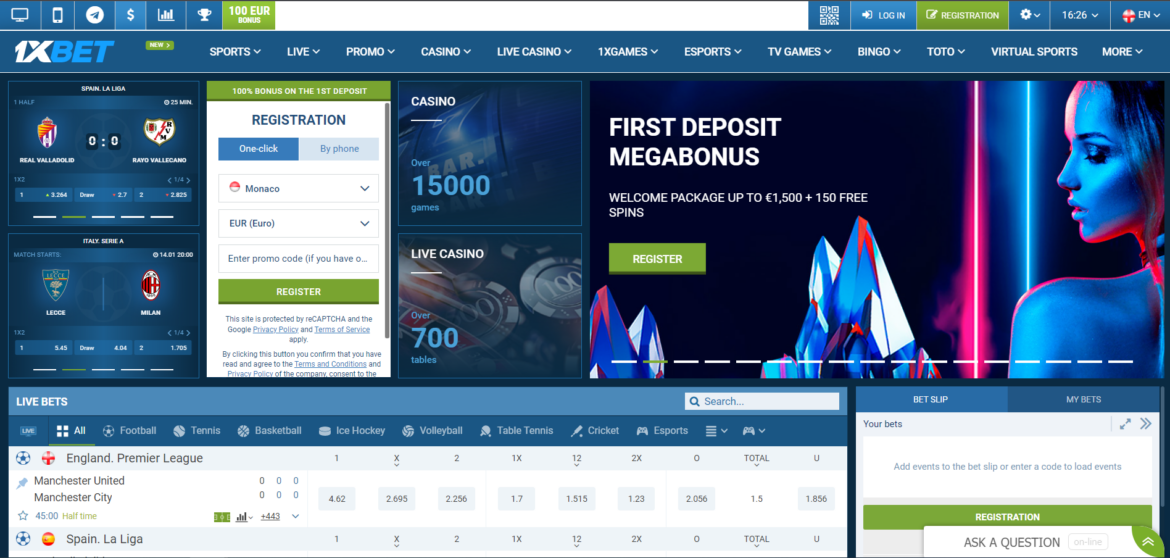
- Extensive betting markets for NBA
- Attractive welcome bonus for new users
- Mobile app available for both Android and iOS.
- User interface can be overwhelming for beginners
- Reports of occasional delay in withdrawals.
22Bet
Launched in 2017 in Russia, 22Bet is rapidly emerging as a major player among bookmakers. They boast a staggering number of sports events and a plethora of payment methods. Their platform is multilingual, currency diverse, and mobile-friendly. If you’re searching for a blend of extensive sports options and user-friendly interfaces, 22Bet might be your ideal match.

- Multiple payment methods, including local options
- Regular odds boost for NBA games
- 24/7 customer support.
- The design of the platform may seem outdated
- Requires verification for large withdrawals.
20bet
Operating under the Betsson banner since 2020, 20BET offers an expansive live betting zone. Their interface simplifies the deposit process, and they support an assortment of payment gateways, including various cryptocurrencies. Their platform is ideal for those seeking a mobile-centric experience combined with attractive bonuses.
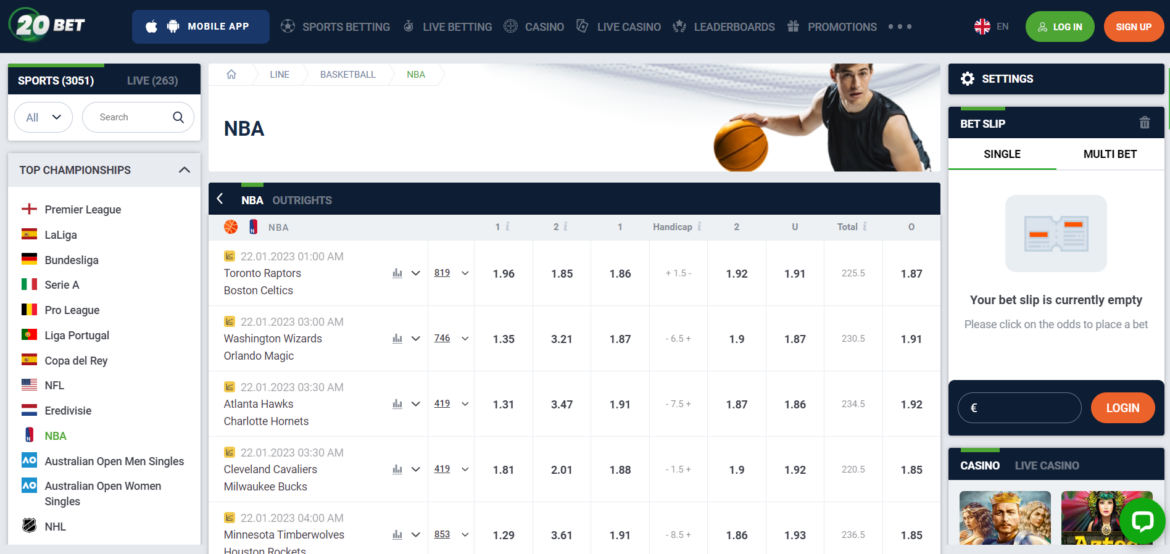
- Seamless in-play betting experience
- Diverse prop bets for NBA games
- Regular tournaments and leaderboards for bettors.
- Limited promotional offers
- No dedicated mobile app.
Betway
With a global presence, Betway provides a plethora of sports betting markets complemented by commendable odds. They also flaunt an extensive selection of casino and live dealer games. Licensed by major regulatory bodies, they ensure user security and provide multiple deposit avenues. If comprehensive sports betting options and safety are your priorities, Betway is a strong contender.
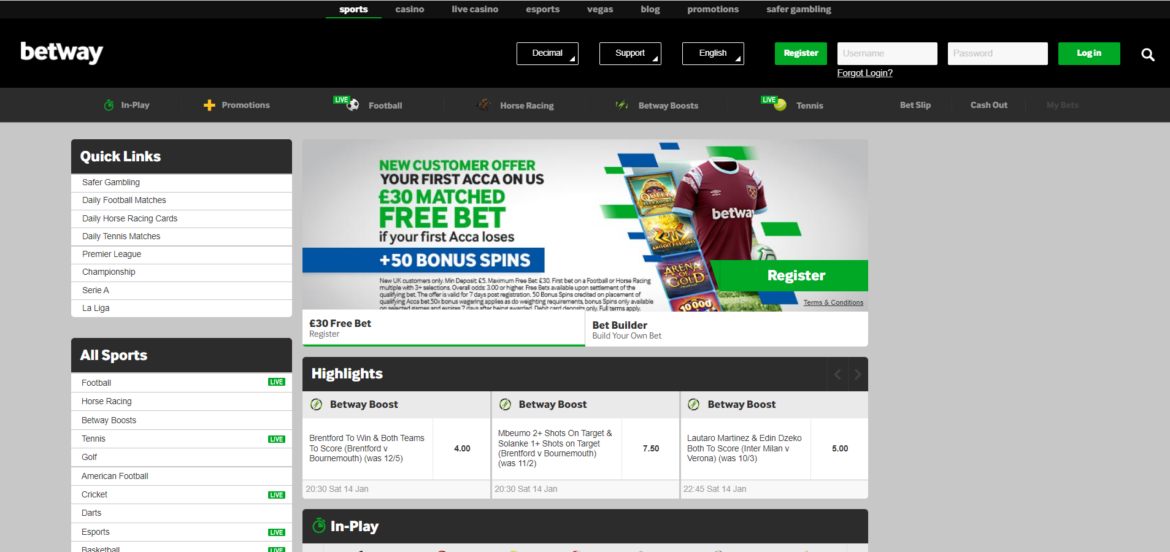
- Reputable brand with a global presence
- Dedicated NBA betting promotions
- In-depth statistics and match insights.
- Limited options for cryptocurrency users
- Withdrawal times can be longer than competitors.
Dafabet
Asian bookmaker Dafabet has a comprehensive selection of sports betting markets, including those for cricket, tennis, basketball, football, and basketball. The website offers live streaming of select athletic events and is available in many different languages. Along with virtual sports and esports betting, Dafabet also features a casino and a live casino component. The bookmaker allows players from several nations, including the UK, India, and Malaysia, and is authorised and governed by the Philippine government. There are apps for iOS and Android devices, and the website is mobile-friendly.
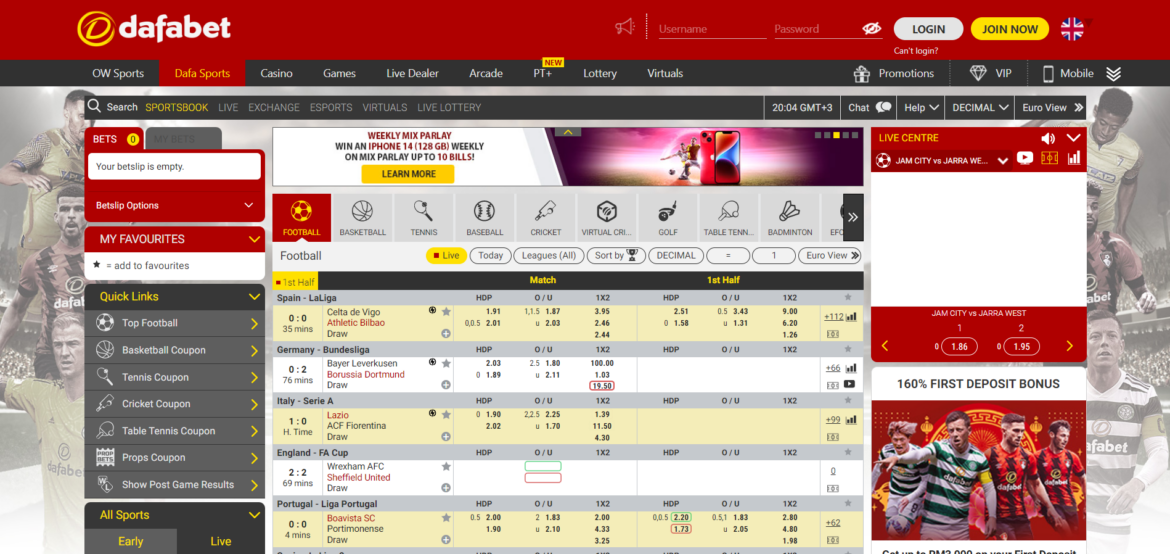
- Focus on Asian markets, including the Philippines
- Generous bonuses and loyalty program
- Offers local payment solutions.
- Website navigation may seem confusing
- Live chat support is not always available.
Betwinner
A prominent online bookmaker, Betwinner is home to over 400,000 users. It offers a spectrum of sports betting options, inclusive of esports, and is recognized for its competitive odds and enticing promotions. The platform boasts live betting, amplifying the thrill of real-time sports events and offering diversified betting alternatives. Their extensive sports coverage, user-friendly interface, robust customer support, and array of payment methods position Betwinner as a top choice for many NBA bettors in the Philippines
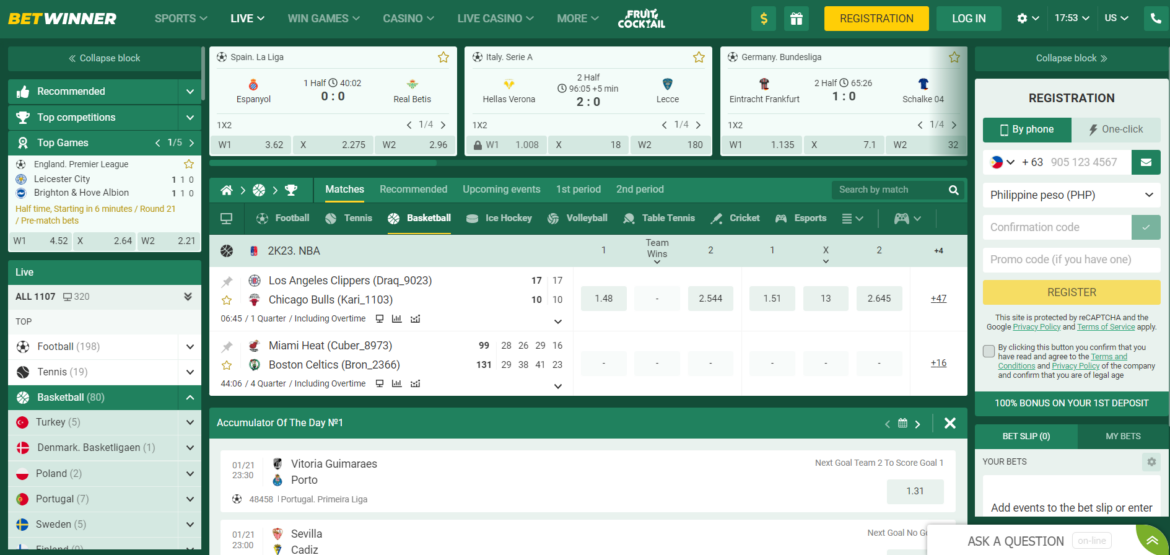
- Comprehensive live betting section
- Offers e-sports NBA 2K betting
- Regular cashback offers.
- The site can be slow during high traffic
- Conversion fees on certain currencies.

Factors to Consider When Choosing a best NBA Online Betting Site
Venturing into NBA online betting requires discernment. It’s crucial to opt for a platform that meets your requirements while ensuring security and pleasure. Here’s a roadmap to help you decide:
- Licensing and Regulation: A betting website’s reliability is crucial. Verify if the platform you’ve chosen has received approval from reputable regulators like the UK Gambling Commission or the Malta Gambling Authority. Such qualifications reflect honest and moral business practises.
- Security Protocols: Your personal and monetary data’s safety is non-negotiable. Prioritize platforms with solid encryption and updated security measures to shield your information.
- Interface and Accessibility: Your betting voyage should be seamless and user-friendly. A platform with an intuitive interface and easy-to-find options enriches the experience and retains users.
- Betting Choices and Odds: Top platforms offer diverse betting categories, spanning from real-time to prop bets. Ensure the platform also provides competitive odds for optimum bet value.
- Payment Options: The platform ought to accept a range of reliable payment options, including cards and e-wallets. Ensure quick transaction times and sensible limits for both deposits and withdrawals.
- Quality Customer Support: Exceptional customer service, available via multiple channels, indicates the platform’s dedication to its users. A proficient support team is pivotal for addressing concerns.
By emphasizing these aspects, you’re on track to identify a platform aligned with your needs, promoting a safe and enjoyable NBA betting journey.
Popular payment methods for NBA betting in the Philippines
For NBA betting in the Philippines, Gcash, PayMaya, and GrabPay are the most popular digital wallets. Their surge in popularity stems from their accessibility, trustworthiness, and ease of use. Moreover, the National Retail Payment System (NRPS) initiative by the Philippine government has promoted retail bank transfers, enhancing B2B transactions nationwide.
Check out other popular Asian and international banking methods for gambling and betting:
See more about Asian Bookmakers
Popular types of bets on NBA games
When betting on NBA games, here are the prevalent options:
- Main Line Bets: A direct wager on the game’s winner.
- Point Differential Bets: Estimating the winning or losing margin.
- Over/Under Bets: Estimating whether the total score will surpass or fall short of the forecast made by the bookmaker.
- Futures Betting: Wagers on forthcoming events, like championship outcomes.
- Basketball Handicap: Betting where the point difference is pivotal. Dive deeper into basketball handicap betting for insights.
It’s essential to highlight that betting rules can differ based on location. So, due diligence is a must before diving into sports betting.
How to Place NBA Bets Online in the Philippines
To place NBA bets online in the Philippines, follow these steps:
- Select a Betting Platform that lists NBA options.
- Register an Account with necessary details like name and email.
- Deposit Funds using the platform’s available payment methods.
- Commence Betting by choosing your preferred type and placing the wager.
Note that Philippine gambling regulations don’t cover licensed offshore bookies, all boasting comprehensive NBA odds and dynamic betting options. Filipinos can wager on NBA odds through accredited offshore outlets or the local bookmaker MegaSportsWorld (MSW). Furthermore, MSW provides an exclusive online sportsbook for VIP patrons aged 21 and up.
Check out other best betting sites for top Asian countries:
Tips for Successful NBA Online Betting
1. Comprehensive Research: To excel in NBA online betting, groundwork is fundamental. Delve deep into the game to grasp NBA’s intricacies, from understanding its rules to staying updated with the latest league happenings.
2. Familiarize with Teams and Players: A comprehensive knowledge of teams and their players is vital. This entails recognizing each team’s strengths and vulnerabilities and being conversant with players’ statistics and past performances.
3. Seek Optimal Odds: Prioritize value by searching for the best odds. It’s beneficial to juxtapose odds from multiple bookmakers. Utilize odds comparison platforms to simplify this task.
4. Prudent Bankroll Management: Effective NBA betting hinges on astute bankroll management. Create a betting budget and stick to it, not risking more money than your means would allow. Spreading your bets also helps to reduce risk.
5. Sidestep Emotional Betting: Impartiality is key. Emotional bets can skew judgment. Ensure your decisions are logical and data-driven, leaning heavily on your research and evaluations.
6. Bet Early: Consider placing your wagers soon after betting markets open, typically around 8-9am EST. This tactic can give you an edge, allowing you to capitalize on fresh intel before the majority.
7. Consider the Game Schedule: Factor in the frequency of games a team plays within a week. Data suggests that teams engaging in 3-4 matches weekly can exhibit fatigue, impacting their consistency, particularly as the season progresses.
By integrating these strategies, you fortify your chances of making more informed and successful NBA online bets.
Conclusion
In the dynamic world of NBA online betting, making informed decisions is key to ensuring both a rewarding and enjoyable experience. From the significance of meticulous research to understanding the nuances of each team and player, and the importance of bankroll management, every strategy plays a crucial role. As the popularity of NBA betting continues to soar in the Philippines, arming oneself with these insights can undoubtedly offer an edge.
FAQ about NBA Online Betting in the Philippines
Yes, NBA online betting is legal in the Philippines provided you bet through licensed and regulated sites.
Digital wallets like Gcash, PayMaya, and GrabPay are popular. The National Retail Payment System (NRPS) of the Philippine government is another factor contributing to the growth of retail bank transfers.
Strategies vary among bettors. However, thorough research, understanding teams and players, seeking optimal odds, and prudent bankroll management are some widely recommended strategies.
Opt for platforms with robust encryption techniques and regularly updated security protocols. Also, always use strong, unique passwords for your accounts.
Yes, many online sports betting platforms offer live betting options, allowing you to place bets as the game unfolds.
Read this page in other languages:





























Your review has been sent for moderation